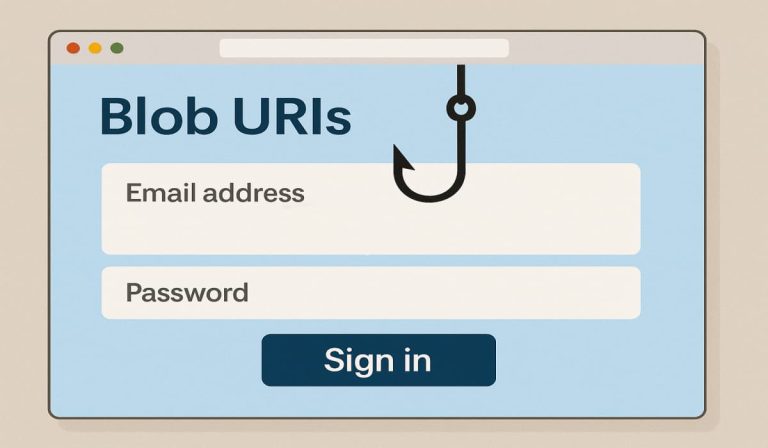
Cofense Intelligence reveals a novel phishing method utilizing blob URIs to create native faux login pages, bypassing e mail safety and stealing credentials.
Cybersecurity researchers at Cofense Intelligence have reported a brand new and more and more efficient technique cybercriminals are utilizing to ship credential phishing pages on to customers’ e mail inboxes. This method, which emerged in mid-2022, leverages “blob URIs” (binary giant objects- Uniform Useful resource Identifiers).
In your info, Blob URIs are addresses that time to non permanent knowledge saved by your web browser by yourself pc. These have legit functions on the web, reminiscent of how YouTube briefly shops video knowledge inside a person’s browser for playback.
A key attribute of blob URIs is their localized nature; that’s, a blob URI created by one browser can’t be accessed by some other, even on the identical gadget. This inherent privateness function though useful for legit internet capabilities, has been weaponized by risk actors for malicious functions.
In accordance with Cofense Intelligence’s evaluation, shared with Hackread.com, since Blob URI knowledge isn’t on the common web, safety methods that examine emails can not simply see the dangerous faux login pages.
Due to this fact, once you get a phishing e mail, the hyperlink doesn’t go straight to a faux web site. As a substitute, it usually sends you to an actual web site that the safety packages belief, like Microsoft’s OneDrive. From there, you get despatched to a hidden webpage managed by the attacker.
This hidden web page then makes use of a blob URI to create the faux login web page proper in your browser. Although this web page is just saved in your pc, it may possibly nonetheless steal your username and password and ship it to the hackers.
This presents a problem for automated safety methods, significantly Safe Electronic mail Gateways (SEGs), which analyze web site content material to establish phishing makes an attempt, researchers famous. The novelty of phishing assaults utilizing blob URIs means AI-powered safety fashions might not but be adequately educated to differentiate between legit and malicious makes use of.
This lack of sample recognition, mixed with the widespread attacker tactic of utilizing a number of redirects, complicates automated detection and will increase the chance of phishing emails bypassing safety.
Cofense Intelligence has noticed a number of phishing campaigns using this blob URI method, with lures designed to trick customers into logging in to faux variations of acquainted providers like OneDrive. These lures embody notifications of encrypted messages, prompts to entry Intuit tax accounts, and alerts from monetary establishments. Regardless of the various preliminary pretexts, the final assault movement stays constant.
Researchers warn that this kind of phishing would possibly grow to be extra widespread as a result of it’s good at getting previous safety. So, it’s necessary to watch out about hyperlinks in emails, even when they seem like they go to actual web sites, and to at all times double-check earlier than you sort in your login info. Seeing “blob:http://” or “blob:https://” within the web site tackle generally is a signal of this new trick.