Regardless of the rise of the info safety market, conventional cybersecurity has lengthy been based mostly on perimeter defenses. The belief was easy: when you’re contained in the community (whether or not via a VPN or bodily entry), you’re trusted.
Firewalls, intrusion preventers, and digital personal networks had been all geared toward this concept of a safe internal world separated from an untrusted outer world.
However with corporations shifting to cloud-first, hybrid work, and multiplexed associate ecosystems, these conventional safety perimeters started to interrupt down. An finish consumer could possibly be sitting in a house workplace, a espresso store, or midway all over the world and nonetheless want entry to enterprise programs in a safe approach.
On the identical time, cyber crimes grew to become extra subtle, exploiting any vulnerability from inside after perimeter safety has been compromised.
What Is Zero Belief Structure?
Zero Belief is a safety framework established on one straightforward precept: by no means belief, all the time confirm.
In contrast to the earlier fashions that by default belief customers and units as soon as contained in the community, Zero Belief tracks every request for entry, the place it’s coming from, what gadget is used, and who the consumer is.
It depends on the presumption that nothing within the system is fully safe by design and frequently authenticates entry via a number of dynamic components.
| Conventional Safety | Zero Belief Structure |
| Trusts inner customers and units | Trusts nobody by default |
| Focuses on perimeter safety | Focuses on id and entry management |
| Flat inner community | Segmented community with least privilege entry |
| Occasional safety checks | Steady verification and monitoring |
How ZTA Differs from Conventional Safety
Core Rules of Zero Belief Structure
A Zero Belief community all the time depends on a well-defined, real-world set of ideas that preserve the system’s safety posture no matter the place customers or units come from.
1. Identification Verification
Earlier than anybody can entry something, their id have to be verified. It’s now not only a password; it’d embody multi-factor authentication (MFA), gadget authentication, and even biometric authentication.
The aim is to make sure that the particular person (or gadget) that’s attempting to attach is certainly who they are saying they’re.
2. Least Privilege Entry
As soon as a person has been authenticated, they’re solely supplied with entry to the precise knowledge or system they should have — nothing extra. This limits potential hurt if an account is ever compromised.
This manner, customers will solely possess adequate privileges to get their work finished, and no extra permissions.
3. Regular Monitoring
A Zero Belief safety mannequin doesn’t cease checking after the primary login. It retains watching in actual time customers’ conduct, the state of units, location, and so forth. If one thing appears suspicious, the system can shut down entry or set off a brand new test.
4. Microsegmentation
As a substitute of getting one large community with every part linked, Zero Belief separates issues into small segments. Every section has its personal set of controls and guidelines. So even when the intruder will get into one section, it might probably’t simply transfer to a different one.
How Zero Belief Safety Structure Works in Observe
Zero Belief isn’t solely a safety precept; it’s a sensible approach of defending programs. Let’s see the way it works in the true world with an instance.
Instance: A Distant Worker Accessing a Firm System
Let’s take the case of a distant employee who must log in to the group’s inner monetary utility.
The worker tries to log in with their username and password.
- Consumer and Gadget Are Verified
Earlier than letting them in, the system checks:
- Is that this actually the suitable particular person? (utilizing, for example, multi-factor authentication)
- Is the gadget protected and accredited? (e.g., up-to-date software program, no indicators of tampering)
- Is the request coming from a safe space?
These checks are regulated by id and entry administration and software-defined perimeter instruments.
- Entry Is Granted However Solely What’s Wanted
If every part seems good, entry is allowed, however solely to what the worker wants. A monetary analyst, for instance, can view experiences however not modify system settings. That is the least privilege precept.
Because the consumer operates, their conduct is adopted in actual time by a safety info and occasion administration (SIEM) system. If one thing fishy occurs (like attempting to obtain massive information or entry restricted zones), entry could be denied or audited.
Even when somebody breaks in, they gained’t get far. Microsegmentation places every a part of the system in an remoted surroundings, so attackers can not merely stroll from one piece to a different.
Instruments That Make It Work
As seen above, Zero Belief entry is constructed on a set of built-in instruments that speak to 1 one other and confirm customers, assure community safety, forestall safety breaches, and monitor exercise in actual time:
- IAM (Identification and Entry Administration): Manages consumer logins and permissions.
- SDP (Software program-Outlined Perimeter): Provides or blocks app entry relying on who customers are and the place they’re from.
- MFA (Multi-Issue Authentication): Incorporates further verifications like a textual content code or app approval.
- SIEM (Safety Info and Occasion Administration): Screens for suspicious conduct in actual time.
Advantages of Zero Belief for Enterprise Techniques
Two years in the past, imposing a Zero Belief structure was a precedence for a majority of corporations.
By 2032, by the way in which, the whole Zero Belief market is believed to be estimated at round $133 billion, up from round $32 billion in 2023. However what are the true, tangible advantages for contemporary enterprise networks?

One of many biggest advantages is that Zero Belief community entry shrinks the assault space. As a result of no consumer and no gadget are trusted by default, every request for entry have to be authenticated.
Which means it’s a lot more durable for attackers to make their approach via the system, even when they do handle to get in.
Additionally, ZTA offers corporations extra management over customers’ entry. As a substitute of mere static consumer roles, Zero Belief takes into consideration all the context (i.e., the particular person’s id, gadget, location, and conduct) to resolve what they need to be capable to see or do.
Third, Zero Belief is visibly efficient for distant and hybrid work. Workers are capable of entry enterprise programs from any location, with out the usage of a VPN or presence within the workplace.
Lastly, Zero Belief supplies higher visibility throughout the system. Since it’s all the time specializing in the consumer and the gadget, safety groups can determine probably malicious exercise early and react rapidly.
Examples of Zero Belief Safety Options in Motion
There are numerous outstanding companies and sectors using Zero Belief Structure to enhance safety whereas permitting distant entry. These examples illustrate how the follow is executed in actual life.
Google’s BeyondCorp is sort of probably essentially the most well-known instance. In response to a serious cyberattack in 2009, Google moved away from counting on VPNs and began engaged on an structure by which entry relies on consumer context and id, not on a community location.
That enabled staff to have the ability to work securely wherever with out essentially having to be on a trusted inner community. BeyondCorp was one of many preliminary real-world Zero Belief architectures.
Microsoft
Microsoft additionally makes use of Zero Belief throughout its Microsoft 365 and Azure options. It depends on sturdy id checks, persistent monitoring, and Conditional Entry and Defender for Identification instruments to handle entry and cease threats in actual time. Customers solely get entry to what they want, and the system watches for uncommon exercise across the clock.
Different Organizations
Many much less outstanding monetary, healthcare, and authorities organizations are additionally adopting Zero Belief. For instance, healthcare amenities management entry to affected person knowledge by position and gadget safety.
Banks divide their networks in such a fashion that if one is attacked, it’s not simply going to unfold to the others. It protects the delicate knowledge with out interrupting clean processes.
Challenges and Issues of Zero Belief Techniques
In 2024, when requested about their intentions to undertake Zero Belief, 30% of respondents (who had been cybersecurity professionals) admitted that they had been working with a number of safety distributors to develop a plan to include Zero Belief and scale back safety dangers.
23% of answerers, in flip, acknowledged they’d already began implementing Zero Belief. Against this, 47% of respondents claimed to not be prepared but to undertake Zero Belief. However why?
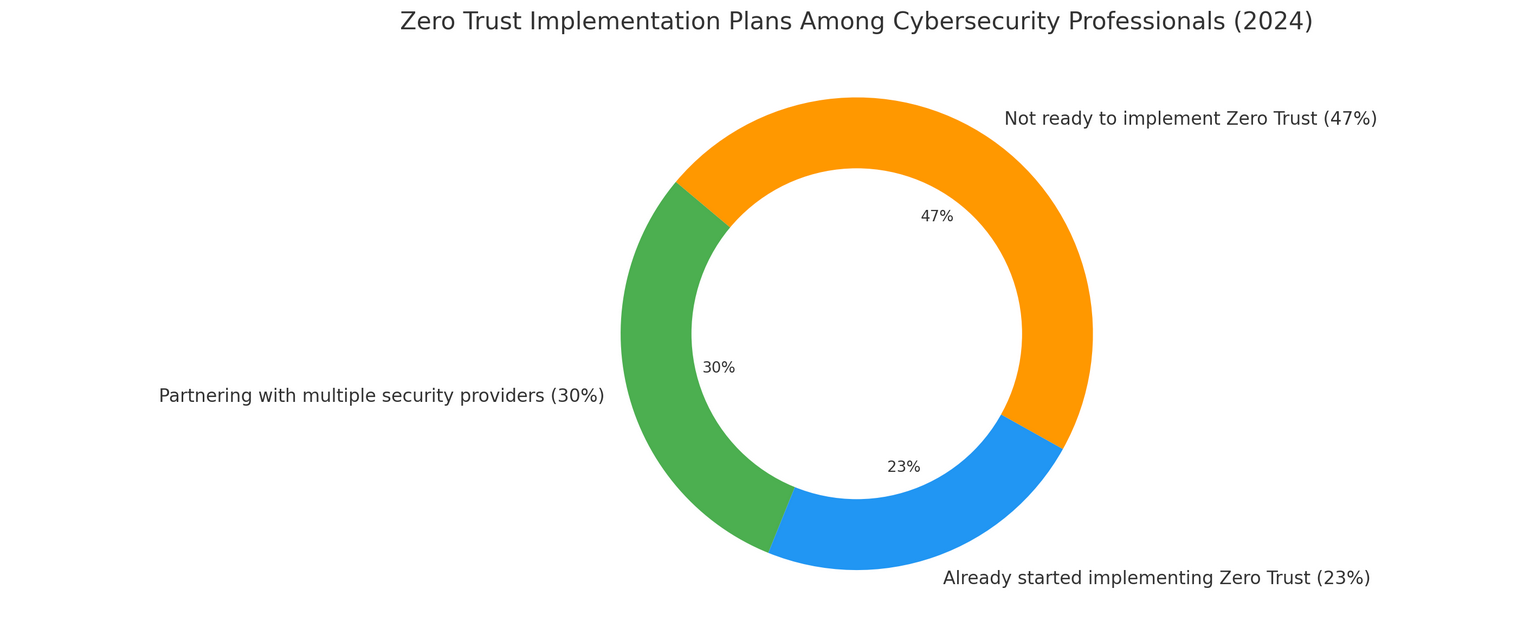
Zero Belief Implementation Amongst Cybersecurity Professionals in 2024
First, Zero Belief usually means rethinking how your programs are constructed. Conventional safety fashions had been based mostly on trusting every part contained in the community.
With Zero Belief, that mannequin adjustments utterly. You’ll want to revamp how customers, units, and purposes join, which can embody reorganizing entry guidelines, segmenting the community, and updating older programs.
Second, you’ll possible have to spend money on new instruments and processes. Zero Belief often entails including id and entry administration, multi-factor authentication, endpoint safety, monitoring instruments, and software-defined perimeter options. These instruments must work collectively, which might take a while and planning.
One other factor is that the Zero Belief surroundings isn’t an install-and-forget configuration. It requires systematic updates: entry insurance policies and safety measures have to be modified when groups develop, roles shift, or new instruments are added.
It additionally requires good communication throughout enterprise models, safety groups, and IT to ensure the system works nicely for all events.
Generally, corporations additionally face resistance to alter. Customers have most likely acquired used to free entry or simplified login processes, and extra stringent controls will subsequently initially look like a nuisance.
That’s the reason it pays to roll out Zero Belief insurance policies in phases, precisely state the explanations for doing so, and supply coaching to your personnel.
How you can Implement Zero Belief Structure
It’s truthful to state that Zero Belief isn’t an instantaneous treatment; it’s a seamless course of. In 2024, most corporations had already began adopting a Zero Belief technique or cooperating with safety distributors to create a roadmap. However how do you start the method in a approach that really works?

The primary factor to recollect earlier than Zero Belief implementation is that placing it into motion doesn’t occur suddenly; it’s a gradual course of that takes cautious planning and the suitable instruments.
Step one is to audit your present surroundings. Which means specifying all customers, endpoints, purposes, and knowledge in your group.
From there, you may start to place extra inflexible id and entry controls in place utilizing options, resembling id and entry administration options and multi-factor authentication.
Subsequent, implement the least privilege precept: customers ought to solely have the entry they really want. No extra. On the identical time, deploy microsegmentation to compartmentalize essentially the most crucial components of your system, so even when one thing goes mistaken, it’s simpler to include the problem.
As you progress ahead, it’s necessary to observe exercise in actual time. Safety info and occasion administration programs can assist you:
- Spot uncommon consumer conduct earlier than it turns into an issue.
- Catch threats early and reply rapidly.
- Replace entry controls mechanically based mostly on altering danger ranges.
We acknowledge that making a complete Zero Belief answer could appear overwhelming, particularly if your organization lacks the in-house sources or obtainable time to do it by yourself.
That’s the place SCAND is available in. We assist organizations develop and implement Zero Belief software program tailored to their actual wants, whether or not you’re greenfielding or upgrading an present implementation.
In tasks involving distant entry, delicate knowledge, or hybrid environments, we:
- Use IAM frameworks to implement least privilege entry.
- Combine MFA and SDP instruments for identity- and context-aware authentication.
- Design infrastructure with microsegmentation, container isolation, and safe APIs.
- Constantly monitor and improve safety insurance policies utilizing SIEM and conduct analytics instruments.
- Apply safe DevOps practices that go according to the Zero Belief strategy, from improvement to deployment.
- Embed generative AI in cybersecurity to additional enhance safety.
Should you rethink your enterprise structure or change to the cloud, now’s the proper second to study Zero Belief ideas. Allow us to hear from you at SCAND and uncover how we can assist you design strong safety programs that may forestall any assaults.
Incessantly Requested Questions (FAQs)
Is Zero Belief just for massive enterprises?
No. Any group can undertake and profit from Zero Belief, particularly in the event that they want cloud safety to help distant work.
Do I have to do away with my VPN and different safety instruments earlier than implementing a Zero Belief system?
Not essentially, however VPNs usually characterize a single level of belief. Zero Belief works as a extra dynamic and safe various.
How lengthy does it take to implement ZTA?
It will depend on your safety infrastructure, however most organizations undertake it steadily, beginning with id and entry safety controls.
Can SCAND assist implement Zero Belief safety programs?
Completely. Whether or not you need to begin from scratch, modernize conventional perimeter-based safety, and even lengthen Zero Belief (if you have already got it), we will supply the suitable strategy for your online business.