Evilginx, a instrument based mostly on the legit (and broadly used) open-source nginx internet server, can be utilized to steal usernames, passwords, and session tokens, permitting an attacker to doubtlessly bypass multifactor authentication (MFA). On this submit, we’ll show how evilginx works and what data it is ready to purchase; we even have recommendation for detecting this instrument in use, in addition to potential mitigations towards its use.
The way it works
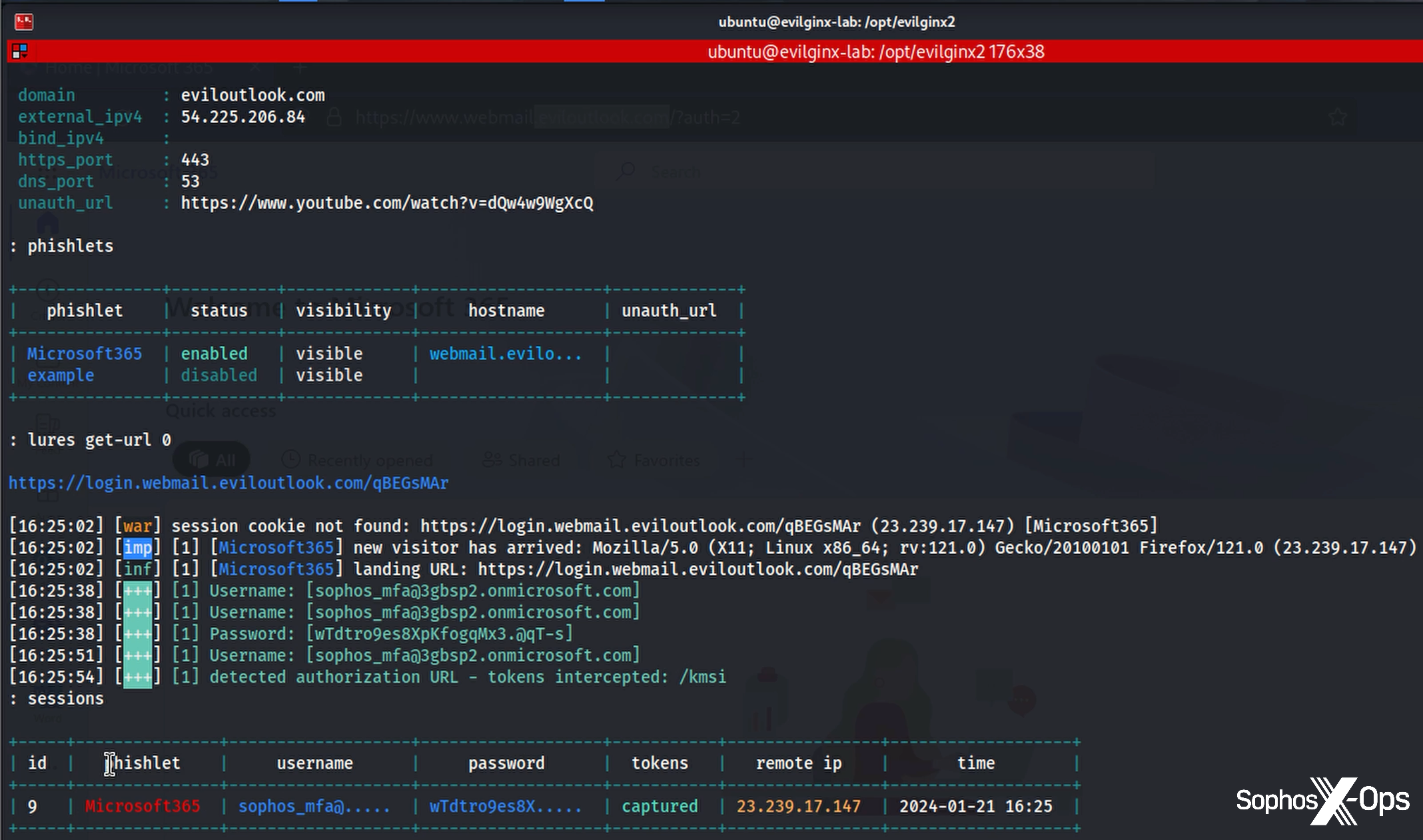
Evilginx at its core makes use of the legit and common internet server nginx to proxy internet visitors by way of malicious websites, created by the risk actor to imitate actual companies reminiscent of Microsoft 365 — an Adversary-in-the-Center (AitM) assault. To show, we configured a malicious area; as proven in Determine 1, we now have a Microsoft phishlet in place with its personal subdomain of that area. (All related IP addresses, usernames, passwords, and domains used on this submit had been decommissioned previous to publication.) The phishlet features a lure, and that lure is what the focused consumer sees because the attacker makes an attempt to seize their username and password.
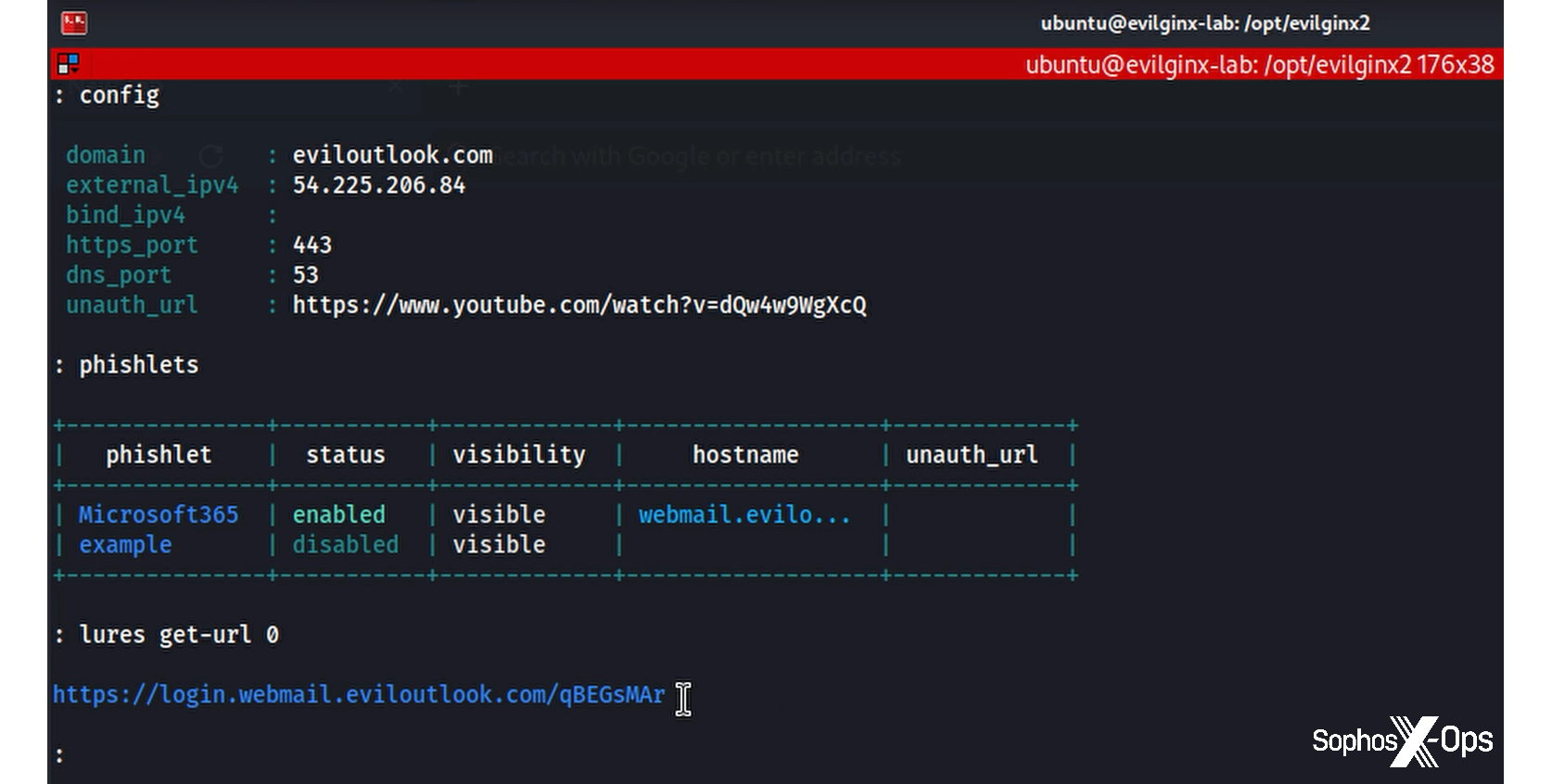
Determine 1: Evilginx in motion, displaying the malicious area, the phishlet, and the lure for use towards the goal
It’s helpful to notice that the types and pictures the consumer sees actually do come from Microsoft itself; they’re relayed from the legit firm by way of the evilginx server and onward to the consumer. On the again finish, evilginx provides the attacker choices for configuring the expertise. In our testing, we mimicked a consumer account protected by MFA… and promptly acquired round it. The consumer is introduced with a “regular” login expertise; it’s solely after they click on on one of many apps alongside the left-hand aspect of the display {that a} canny consumer would possibly discover one thing is odd, as they are going to be requested to login once more.
A have a look at our evilginx server exhibits what’s occurring.
Determine 2: An evilginx server shows captured data and provides it to its database for later abuse
Along with intercepting the consumer’s username and password, the session token was additionally gathered because it was handed from the Maintain Me Signed In performance chosen by the attacker when the Microsoft immediate appeared. Evilginx stashes this information in a database that collects the data on every session, additionally together with the general public IP deal with used to entry the server, the consumer agent in play – and, crucially, the cookie. With this in hand, the attacker want solely open a window to the legit login web page and import the cookie to be signed in because the legit consumer.
From right here, the risk actor has full entry to the consumer’s mailbox account. Typical actions can embody including mailbox guidelines. If entry is out there, the risk actor can even reset MFA units, change passwords, and carry out numerous different actions to provide themselves extra persistence to the account.
Detection avenues
There are numerous methods defenders would possibly uncover exercise of this kind. First, in Azure and Microsoft 365, there are two essential places that preserve observe of logs and occasions that may be reviewed for uncommon exercise. The primary are the Entra ID (beforehand often known as Azure AD) check in and Audit logs. The 2 examples in Determine 3 present our customers’ authentications originating from our evilginx server (54.225.206.84), after which from the Tor exit node that we used for our demonstration (45.80.158.27). The audit logs present that after this login, our attacker added a brand new authenticator app to “their” account.
Determine 3: There may be positively nothing suspicious about an inbox rule named Fully Reliable Forwarder
Second, the Microsoft 365 logs, additionally referred to as the unified audit log or UAL, present that through the session our illegitimate consumer added a brand new inbox rule referred to as Fully Legit Forwarder. (To help with reviewing these logs, Microsoft 365 additionally gives a sophisticated searching space inside the safety middle that permits you to use the Kusto question language to filter and discover suspicious exercise utilizing totally different standards.)
Safety alerts and incidents are additionally generated when suspicious exercise is detected. For example, we will see in Determine 4 that the sophos_mfa account tried to check in from a suspicious IP deal with, and that an anomalous token was used throughout a kind of periods.
Determine 4: The anomalous token, the nameless IP deal with, and the suspicious redirect rule are all flagged
For Sophos prospects, integrations exist for importing occasions and alerts from Azure and Microsoft 365 into Sophos Central. Relying on the particular XDR integration pack, customized identity-related detections are a part of the bundle; for MDR prospects, these detections are triaged by the MDR workforce as a part of the service.
Potential mitigations and considerations
Potential mitigations could be sorted into two classes, preemptive and reactive. A full checklist of potential mitigations is properly past the scope of this text, however as ever, a thought-out and layered strategy is finest relating to defending any form of functions or companies which might be publicly accessible and of excessive worth in your surroundings.
Nonetheless, it’s time we as an business look to stronger measures, migrating off token-based or push MFA and towards sturdy, phishing-resistant, FIDO2-based authentication strategies.
The excellent news is that good choices can be found in lots of types – Yubikey-type {hardware} keys, Apple Contact ID on trendy {hardware}, Home windows Good day for enterprise, even choices that incorporate iPhone and Android. (For additional ideas on higher instructions in MFA, please see Chester Wisniewski’s latest essay on passkeys.)
Conditional entry insurance policies are one other potential step for securing your Azure and Microsoft 365 environments. In idea in fact one may take the old style, hand-crafted whitelist route – blocking any IP deal with that’s not trusted – however virtually talking it’s the units one would handle, permitting solely enterprise-trusted units to log into enterprise programs. (Sophos and different distributors in fact do preserve fixed look ahead to, and block, known-malicious websites as a part of our companies — a endless process, and blocklisting is arguably simpler to handle than whitelisting.)
That mentioned, we can’t in the end depend on consumer consciousness. People are fallible, and actually everybody will ultimately be phished. The trail ahead lies with architectures which might be resilient when people fail.
For reactive mitigations, step one ought to be to shut the door on the risk actor. On this case, there are a selection of steps that ought to be taken to verify the door is absolutely closed. To start out, revoke all periods and tokens by way of Entra ID and Microsoft 365, to take away entry that has been gained. These actions could be carried out within the consumer’s account in each Entra ID and Microsoft 365 utilizing the “Revoke periods” and “Signal out of all periods” buttons.
Subsequent, reset the consumer’s passwords and MFA units. As we noticed within the logs, our risk actor added a brand new MFA gadget to the consumer’s account. Relying on the kind of MFA gadget added, this will permit passwordless entry to the account, eradicating the efficacy of fixing passwords and eradicating periods. Use Microsoft 365’s logs to look at all exercise undertaken by the attacker. Recognizing stealth modifications, such because the addition of latest inbox guidelines, is vital to verify no extra data is ready to depart the consumer’s account. Directors might discover it helpful to refer additionally to Microsoft’s personal investigation steerage regarding token theft.
Conclusion
Evilginx is a formidable methodology of MFA-bypassing credential compromise — and it makes a posh assault method workable, which in flip can result in widespread use of the method. The excellent news is that the mitigations and practices it’s best to already be following are highly effective deterrents to the success of attackers trying to deploy this instrument towards your infrastructure.