Here is what to learn about malware that raids e mail accounts, net browsers, crypto wallets, and extra – all in a quest to your delicate information
16 Apr 2025
•
,
6 min. learn

On this planet of cybercrime, info is a method to an finish. And that finish, most of the time, is to earn a living. That’s why information-stealing (infostealer) malware has risen to grow to be a significant driver of id fraud, account takeover and digital forex theft. However there are additionally loads of those who stay a lot of their every day lives on-line and handle to remain protected. The secret is to grasp learn how to handle digital danger successfully.
Right here’s what it is advisable to know to maintain your private and monetary info out of hurt’s approach.
What sort of data do infostealers steal?
Many infostealers could hint their roots again to an “iconic” little bit of malware: a banking Trojan often known as ZeuS that was designed to covertly steal victims’ monetary info, resembling on-line banking logins. When its supply code was leaked in 2011, new variations flooded the cybercrime underground and the burgeoning infostealer business started in earnest, with builders upgrading and customizing its capabilities. At the moment there are variations constructed for almost each computing platform, from Home windows PCs and macOS computer systems to iOS and Android gadgets.
What infostealers are after is determined by the variant. Logins, and session cookies, which might allow hackers to bypass multifactor authentication (MFA), are a well-liked goal. One report estimates that 75% (2.1 billion) of the three.2 billion credentials stolen final 12 months had been harvested through infostealers. Different private and monetary info that could possibly be in danger consists of:
- Cost card, checking account and cryptocurrency particulars (e.g., crypto pockets keys)
- Different monetary info, together with insurance coverage or authorities welfare (Social Safety) particulars
- Browser information together with looking historical past and any “saved type” information, which might embrace fee particulars and passwords
- System details about your laptop or system
- Recordsdata saved in your machine/system together with photographs and paperwork
- Different private info together with names, cellphone numbers and addresses
How do infostealers work?
The purpose of the malware is to silently and quickly discover delicate info in your machine or system after which exfiltrate it to a server underneath the management of your attackers. It’ll achieve this by raiding net browsers, e mail shoppers, crypto wallets, recordsdata, purposes and the working system itself. Different strategies embrace:
- “Type grabbing,” which entails looking for logins that you could have entered into a web based type, earlier than it’s ship to a safe server
- Keylogging, which requires the malware to document each keystroke you make
- Taking screenshots of your private home display screen/desktop in case any delicate info is displayed there
- Stealing info from the machine’s clipboard
As soon as the knowledge has been despatched again to an adversary’s server, typically inside seconds, they usually bundle it up into logs and promote it on the cybercrime underground. Fraudsters will then use it to:
- Hijack your on-line accounts (e.g., Netflix, Uber) with a view to stealing info saved inside and/or promoting entry to others
- Commit id fraud, resembling making use of for credit score in your title, or utilizing your playing cards/checking account to buy objects
- Commit medical/insurance coverage fraud by acquiring medical remedy/medicine in your title
- Commit tax fraud, by submitting tax returns in your title and receiving refunds
- Goal your contacts with phishing messages or spam
- Drain your monetary accounts of funds
How do I get compromised with infostealers?
Step one in direction of staying protected from infostealers is knowing how they unfold. There are numerous vectors for assault, however the most typical embrace:
- Phishing emails/texts: A basic social engineering method to steer you to click on on malicious hyperlinks or open an attachment, triggering a covert malware set up. The menace actor will often impersonate a trusted individual, model or authority, together with spoofing the sender area and that includes official logos.
- Malicious web sites: These could also be used as a part of a phishing marketing campaign or as a standalone “asset”. It’s possible you’ll be inspired to obtain/click on on a hyperlink, or the location would possibly set off a “drive-by-download” just by visiting it. Risk actors might use black hat search engine marketing strategies to artificially elevate these websites to the highest of the search rankings, so that they’re extra more likely to seem once you search for one thing on-line.
- Compromised web sites: Generally, hackers compromise respectable web sites that you just would possibly go to, by probably exploiting a browser vulnerability or inserting a malicious advert (malvertising). Each strategies might set off an infostealer set up.
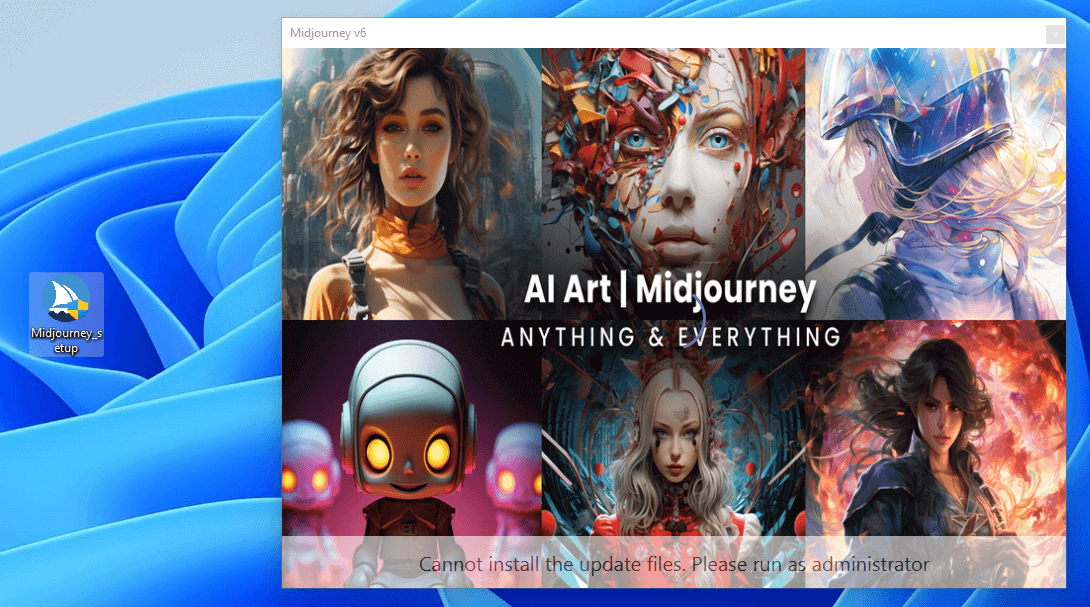
- Malicious apps: Reliable-looking software program could disguise a nasty info-stealing shock when downloaded. The chance is especially acute for cellular gadgets that always aren’t protected in addition to computer systems. Be careful particularly for pirated variations of fashionable video games and different software program.
- Social scams: Scammers could attempt to trick you into clicking via on an attractive social media advert or submit, probably by impersonating a star and even hijacking a respectable account. Beware affords, prize attracts and unique content material that appear too good to be true.
- Sport mods/cheats: Unofficial modifications or cheats for video video games could comprise infostealer malware. In truth, ESET researchers discovered a number of GitHub repositories claiming to supply farm bots and auto-clickers designed to hurry up gameplay on Hamster Kombat. In actuality, they had been hiding the Lumma Stealer variant.
Peering into the menace panorama
As ESET reveals in its H2 2024 Risk Report the infostealer market is massive enterprise for cybercriminals. The malware-as-a-service (MaaS) mannequin has democratized entry to most of the infostealer variants obtainable on legal marketplaces. A few of these websites additionally supply log parsing companies to assist cybercriminals extract information from uncooked logs to be used or resale.
As ESET observes, these items of malware are underneath fixed improvement. Formbook, for instance, has been in operation since 2021. However most just lately, it has added refined obfuscation strategies, designed to make sampling and evaluation by safety researchers tougher. Different variants, like RedLine, have disappeared as a consequence of coordinated legislation enforcement motion. However others, resembling Lumma Stealer, merely transfer in to take their place. This variant recorded a 369% annual improve in detections in H2 2024, in line with ESET analysis.
How do I keep away from infostealers?
So how will you be sure an infostealer doesn’t find yourself in your cellular system or laptop? On condition that the malware may be unfold through a number of strategies, you’ll want to recollect a number of greatest practices. These embrace:
- Set up and preserve safety software program up to date on all of your gadgets. This can go an extended approach to conserving you protected from infostealers and different threats.
- Be phishing-aware, which signifies that you need to keep away from clicking on hyperlinks in any unsolicited messages or open attachments. At all times verify with the sender independently that they positively despatched you the message. Generally, hovering above the “sender” area could reveal that an e mail was in truth despatched by another person.
- Solely obtain software program/apps from official on-line shops. Though malware generally creeps onto Google Play, it’s often taken down swiftly, and these official channels are approach safer than third-party shops. Additionally, keep away from downloading any pirated or cracked software program, particularly if it’s supplied without cost.
- Hold OS and apps updated, as a result of the newest software program model can even be probably the most safe.
- Use warning on social media and keep in mind that if a suggestion appears too good to be true, it often is. If you happen to’re suspicious, attempt Googling it to see if it might be a rip-off. And keep in mind that the accounts of associates and celebrities will also be hijacked to advertise scams. Keep away from clicking on any unsolicited hyperlinks.
- Improve safety at login by utilizing sturdy, distinctive passwords for every account, saved in a password supervisor. And change on multi-factor authentication (MFA) for all your accounts. This can supply some safety towards sure infostealer strategies resembling keylogging, though it isn’t 100% foolproof.
The trick is to layer up these measures, thus lowering the avenues for assault open to menace actors. However bear in mind too that they are going to proceed to try to develop new workarounds, so vigilance is vital.