Cybersecurity researchers have uncovered the interior workings of an Android malware referred to as AntiDot that has compromised over 3,775 units as a part of 273 distinctive campaigns.
“Operated by the financially motivated risk actor LARVA-398, AntiDot is actively offered as a Malware-as-a-Service (MaaS) on underground boards and has been linked to a variety of cellular campaigns,” PRODAFT stated in a report shared with The Hacker Information.
AntiDot is marketed as a “three-in-one” resolution with capabilities to document the machine display by abusing Android’s accessibility providers, intercept SMS messages, and extract delicate information from third-party purposes.
The Android botnet is suspected to be delivered through malicious promoting networks or by way of extremely tailor-made phishing campaigns based mostly on exercise that signifies selective concentrating on of victims based mostly on language and geographic location.
AntiDot was first publicly documented in Might 2024 after it was noticed being distributed as Google Play updates to perform its data theft aims.
Like different Android trojans, it options a variety of capabilities to conduct overlay assaults, log keystrokes, and remotely management contaminated units utilizing Android’s MediaProjection API. It additionally establishes a WebSocket communication to facilitate real-time, bi-directional communication between the contaminated machine and an exterior server.
In December 2024, Zimperium revealed particulars of a cellular phishing marketing campaign that distributed an up to date model of AntiDot dubbed AppLite Banker utilizing job offer-themed decoys.
The newest findings from the Swiss cybersecurity firm present that there are at the least 11 energetic command-and-control (C2) servers in operation which can be overseeing a minimum of 3,775 contaminated units throughout 273 distinct campaigns.
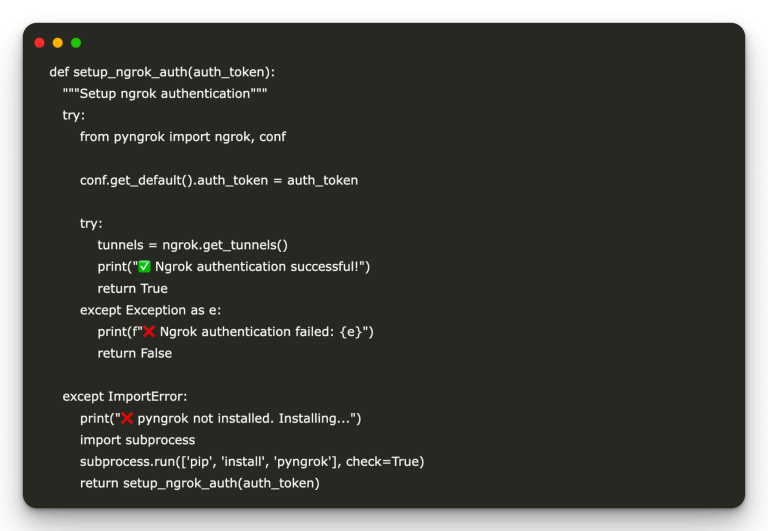
A Java-based malware at its core, AntiDot is closely obfuscated utilizing a industrial packer to sidestep detection and evaluation efforts. The malware, per PRODAFT, is delivered as a part of a three-stage course of that begins with an APK file.
“An inspection of the AndroidManifest file reveals that many class names don’t seem within the authentic APK,” the corporate stated. “These lacking lessons are dynamically loaded by the packer throughout set up, and embody malicious code extracted from an encrypted file. All the mechanism is deliberately crafted to keep away from detection by antivirus instruments.”
As soon as launched, it serves a bogus replace bar and prompts the sufferer to grant it accessibility permissions, after which it unpacks and masses a DEX file incorporating the botnet features.
A core function of AntiDot is its capacity to observe for newly launched purposes and serve and serve a bogus login display from the C2 server when the sufferer opens a cryptocurrency- or payment-related app that the operators are excited about.
The malware additionally abuses accessibility providers to collect intensive details about the contents of the energetic screens and units itself because the default SMS app for capturing incoming and outgoing texts. Moreover, it may possibly monitor telephone calls, block calls from particular numbers, or redirect them, successfully opening up extra avenues for fraud.
One other necessary function is that it may possibly maintain monitor of real-time notifications displayed within the machine’s standing bar and takes steps to both dismiss or snooze them in a bid to suppress alerts and keep away from alerting the consumer of suspicious exercise.
PRODAFT stated the C2 panel that powers the distant management features is constructed utilizing MeteorJS, an open-source JavaScript framework that allows real-time communication. The panel has six completely different tabs –
- Bots, which shows a listing of all of the compromised units and their particulars
- Injects, which shows a listing of all goal apps for overlay injection and consider the overlay template for every inject
- Analytic, which shows a listing of purposes put in on sufferer units and sure used to determine new and in style apps for future concentrating on
- Settings, which accommodates the core configuration choices for the panel, together with updating the injects
- Gates, which is used to handle the infrastructure endpoints that the bots connect with
- Assist, which presents help sources for utilizing the malware
“AntiDot represents a scalable and evasive MaaS platform designed for monetary achieve by way of persistent management of cellular units, particularly in localized and language-specific areas,” the corporate stated. “The malware additionally employs WebView injection and overlay assaults to steal credentials, making it a critical risk to consumer privateness and machine safety.”
GodFather Returns
The event arrives as Zimperium zLabs stated it uncovered a “refined evolution” of the GodFather Android banking trojan that makes use of on-device virtualization to hijack authentic cellular banking and cryptocurrency purposes and perform real-time fraud.
“The core of this novel approach is the malware’s capacity to create an entire, remoted digital setting on the sufferer’s machine. As a substitute of merely mimicking a login display, the malware installs a malicious ‘host’ software that accommodates a virtualization framework,” researchers Fernando Ortega and Vishnu Pratapagiri stated.
“This host then downloads and runs a replica of the particular focused banking or cryptocurrency app inside its managed sandbox.”
Ought to the sufferer launch the app, they’re redirected to the digital occasion, from the place their actions are monitored by the risk actors. As well as, the most recent model of GodFather packs in options to bypass static evaluation instruments by making use of ZIP manipulation and filling the AndroidManifest file with irrelevant permissions.
Like within the case of AntiDot, GodFather depends on accessibility providers to conduct its data gathering actions and management compromised units. Whereas Google has enforced safety protections that forestall sideloaded apps from enabling accessibility providers beginning Android 13, a session-based set up method can get round this safeguard.
The session-based methodology is utilized by Android app shops to deal with app set up, as do texting apps, mail shoppers, and browsers when offered with APK information.
Central to the functioning of the malware is its virtualization function. Within the first stage, it collects details about the listing of put in apps and checks if it consists of any of the predetermined apps it is configured to focus on.
If matches are discovered, it extracts related data from these apps after which proceeds to put in a replica of these apps in a digital setting contained in the dropper app. Thus when the sufferer makes an attempt to launch the precise banking software on their machine, GodFather intercepts the motion and opens the virtualized occasion as an alternative.
It is price mentioning that comparable virtualization options had been beforehand flagged in one other Android malware codenamed FjordPhantom, which was documented by Promon in December 2023. The strategy represents a paradigm shift in cellular risk capabilities that transcend the standard overlay tactic to steal credentials and different delicate information.
“Whereas this GodFather marketing campaign casts a large internet, concentrating on practically 500 purposes globally, our evaluation reveals that this extremely refined virtualization assault is at the moment centered on a dozen Turkish monetary establishments,” the corporate stated.
“A very alarming functionality uncovered within the GodFather malware is its capability to steal machine lock credentials, regardless of whether or not the sufferer makes use of an unlock sample, a PIN, or a password. This poses a big risk to consumer privateness and machine safety.”
The cellular safety firm stated the abuse of accessibility providers is without doubt one of the some ways malicious apps can obtain privilege escalation on Android, permitting them to acquire permissions that exceed their practical necessities. These embody misuse of Unique Tools Producer (OEM) permissions and safety vulnerabilities in pre-installed apps that can’t be eliminated by customers.
“Stopping privilege escalation and securing Android ecosystems in opposition to malicious or over-privileged purposes requires greater than consumer consciousness or reactive patching — it calls for proactive, scalable, and clever protection mechanisms,” safety researcher Ziv Zeira stated.
SuperCard X Malware Involves Russia
The findings additionally comply with the primary recorded makes an attempt to focus on Russian customers with SuperCard X, a newly emerged Android malware that may conduct near-field communication (NFC) relay assaults for conducting fraudulent transactions.
Based on Russian cybersecurity firm F6, SuperCard X is a malicious modification of a authentic software referred to as NFCGate that may seize or modify NFC visitors. The top purpose of the malware is to not solely obtain NFC visitors from the sufferer, but in addition financial institution card information learn by sending instructions to its EMV chip.
“This software permits attackers to steal financial institution card information by intercepting NFC visitors for subsequent theft of cash from customers’ financial institution accounts,” F6 researcher Alexander Koposov stated in a report revealed this week.
Assaults leveraging SuperCard X had been first noticed concentrating on Android customers in Italy earlier this 12 months, weaponizing NFC expertise to relay information from victims’ bodily playing cards to attacker-controlled units, from the place they had been used to hold out fraudulent ATM withdrawals or authorize point-of-sale (PoS) funds.
The Chinese language-speaking MaaS platform, marketed on Telegram as able to concentrating on prospects of main banks within the U.S., Australia and Europe, shares substantial code-level overlaps with NGate, an Android malware that has additionally been discovered weaponizing NFCGate for malicious functions within the Czech Republic.
All these campaigns are united by the truth that they depend on smishing methods to persuade a possible sufferer of the necessity to set up an APK file on the machine below the guise of a helpful program.
Malicious Apps Noticed on App Shops
Whereas the entire aforementioned malware strains require victims to sideload the apps on their units, new analysis has additionally unearthed malicious apps on the official Google Play Retailer and Apple’s App Retailer with capabilities to harvest private data and steal mnemonic phrases related to cryptocurrency wallets with the purpose of draining their belongings.
One of many apps in query, RapiPlata, is estimated to have been downloaded round 150,000 instances on each Android and iOS units, underscoring the severity of the risk. The app is a kind of malware referred to as SpyLoan, which lures customers by claiming to supply loans at low-interest charges, solely to be subjected to extortion, blackmail, and information theft.
“RapiPlata primarily targets Colombian customers by promising fast loans,” Examine Level stated. “Past its predatory lending practices, the app engages in intensive information theft. The app had intensive entry to delicate consumer information — together with SMS messages, name logs, calendar occasions, and put in purposes — even going as far as to add this information to its servers.”
The cryptocurrency pockets phishing apps, alternatively, have been distributed by way of compromised developer accounts and serve a phishing web page through WebView to acquire the seed phrases.
Though these apps have since been faraway from the respective app shops, the hazard is that the Android apps might be obtainable for obtain from third-party app marketplaces. Customers are suggested to train warning when downloading monetary or loan-related purposes.