Safety researchers not too long ago revealed that the non-public data of thousands and thousands of people that utilized for jobs at McDonald’s was uncovered after they guessed the password (“123456”) for the quick meals chain’s account at Paradox.ai, an organization that makes synthetic intelligence based mostly hiring chatbots utilized by many Fortune 500 companies. Paradox.ai mentioned the safety oversight was an remoted incident that didn’t have an effect on its different prospects, however latest safety breaches involving its staff in Vietnam inform a extra nuanced story.

A screenshot of the paradox.ai homepage exhibiting its AI hiring chatbot “Olivia” interacting with potential hires.
Earlier this month, safety researchers Ian Carroll and Sam Curry wrote about easy strategies they discovered to entry the backend of the AI chatbot platform on McHire.com, the McDonald’s web site that lots of its franchisees use to display screen job candidates. As first reported by Wired, the researchers found that the weak password utilized by Paradox uncovered 64 million data, together with candidates’ names, e mail addresses and cellphone numbers.
Paradox.ai acknowledged the researchers’ findings however mentioned the corporate’s different shopper situations weren’t affected, and that no delicate data — reminiscent of Social Safety numbers — was uncovered.
“We’re assured, based mostly on our data, this check account was not accessed by any third get together apart from the safety researchers,” the corporate wrote in a July 9 weblog submit. “It had not been logged into since 2019 and albeit, ought to have been decommissioned. We wish to be very clear that whereas the researchers could have briefly had entry to the system containing all chat interactions (NOT job purposes), they solely seen and downloaded 5 chats in whole that had candidate data inside. Once more, at no level was any information leaked on-line or made public.”
Nevertheless, a assessment of stolen password information gathered by a number of breach-tracking companies exhibits that on the finish of June 2025, a Paradox.ai administrator in Vietnam suffered a malware compromise on their system that stole usernames and passwords for quite a lot of inside and third-party on-line companies. The outcomes weren’t fairly.
The password information from the Paradox.ai developer was stolen by a malware pressure often called “Nexus Stealer,” a type grabber and password stealer that’s bought on cybercrime boards. The data snarfed by stealers like Nexus is commonly recovered and listed by information leak aggregator companies like Intelligence X, which studies that the malware on the Paradox.ai developer’s system uncovered a whole lot of largely poor and recycled passwords (utilizing the identical base password however barely completely different characters on the finish).
These purloined credentials present the developer in query at one level used the identical seven-digit password to log in to Paradox.ai accounts for quite a few Fortune 500 companies listed as prospects on the corporate’s web site, together with Aramark, Lockheed Martin, Lowes, and Pepsi.
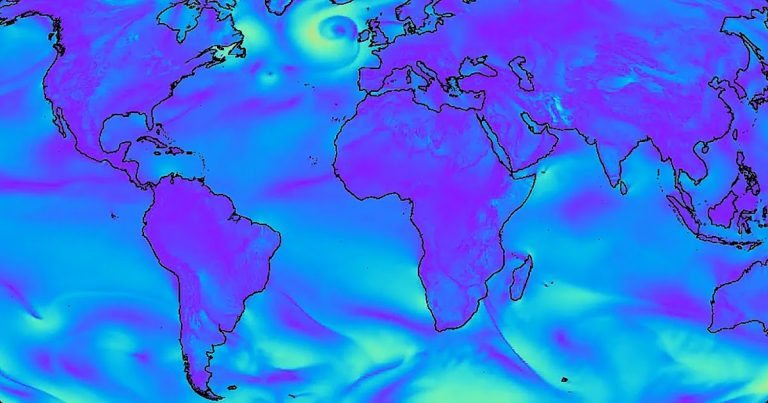
Seven-character passwords, significantly these consisting completely of numerals, are extremely weak to “brute-force” assaults that may strive a lot of doable password combos in fast succession. In accordance with a much-referenced password power information maintained by Hive Programs, trendy password-cracking techniques can work out a seven quantity password roughly immediately.

Picture: hivesystems.com.
In response to questions from KrebsOnSecurity, Paradox.ai confirmed that the password information was not too long ago stolen by a malware an infection on the non-public system of a longtime Paradox developer based mostly in Vietnam, and mentioned the corporate was made conscious of the compromise shortly after it occurred. Paradox maintains that few of the uncovered passwords have been nonetheless legitimate, and {that a} majority of them have been current on the worker’s private system solely as a result of he had migrated the contents of a password supervisor from an previous laptop.
Paradox additionally identified that it has been requiring single sign-on (SSO) authentication since 2020 that enforces multi-factor authentication for its companions. Nonetheless, a assessment of the uncovered passwords exhibits they included the Vietnamese administrator’s credentials to the corporate’s SSO platform — paradoxai.okta.com. The password for that account led to 202506 — presumably a reference to the month of June 2025 — and the digital cookie left behind after a profitable Okta login with these credentials says it was legitimate till December 2025.
Additionally uncovered have been the administrator’s credentials and authentication cookies for an account at Atlassian, a platform made for software program improvement and mission administration. The expiration date for that authentication token likewise was December 2025.
Infostealer infections are among the many main causes of knowledge breaches and ransomware assaults at present, and so they consequence within the theft of saved passwords and any credentials the sufferer varieties right into a browser. Most infostealer malware additionally will siphon authentication cookies saved on the sufferer’s system, and relying on how these tokens are configured thieves might be able to use them to bypass login prompts and/or multi-factor authentication.
Very often these infostealer infections will open a backdoor on the sufferer’s system that permits attackers to entry the contaminated machine remotely. Certainly, it seems that distant entry to the Paradox administrator’s compromised system was provided on the market not too long ago.
In February 2019, Paradox.ai introduced it had efficiently accomplished audits for 2 pretty complete safety requirements (ISO 27001 and SOC 2 Sort II). In the meantime, the corporate’s safety disclosure this month says the check account with the atrocious 123456 username and password was final accessed in 2019, however one way or the other missed of their annual penetration exams. So how did it handle to move such stringent safety audits with these practices in place?
Paradox.ai instructed KrebsOnSecurity that on the time of the 2019 audit, the corporate’s varied contractors weren’t held to the identical safety requirements the corporate practices internally. Paradox emphasised that this has modified, and that it has up to date its safety and password necessities a number of instances since then.
It’s unclear how the Paradox developer in Vietnam contaminated his laptop with malware, however a better assessment finds a Home windows system for one more Paradox.ai worker from Vietnam was compromised by comparable data-stealing malware on the finish of 2024 (that compromise included the sufferer’s GitHub credentials). Within the case of each staff, the stolen credential information contains Internet browser logs that point out the victims repeatedly downloaded pirated motion pictures and tv exhibits, which are sometimes bundled with malware disguised as a video codec wanted to view the pirated content material.